We have Technologies that Know How to Stop and End Threats, Better
Is your data secured? Are your mobile and web applications safe??
Bitter Fact: Threats are becoming more aggressive. Budgets are tight while skills are at an all-time high premium. Business essentials like applications, big data, mobility and social media can pose serious threats, inadequacies and risks in case, in case, they are not properly managed. Ameya Infocom can help you resolve these grave challenges and bridge the gap – via unequaled threat intelligence, flexible application security services and integrated technologies designed to meet the specific demands of your organization.
Adopt Our Unsurpassable software and Application Security Practices throughout the Software Development Lifecycle to Avert Costly Business Interruptions and Critical Data Loss!
Today, business applications continue to be one of the critical factors of enterprise risks. The applications devised to boost efficiency and simplify collaboration may leave business susceptible to data loss. A rational and proactive approach for developing and monitoring an application security program renders ability to address and prevent increasingly hostile attacks while maneuvering compliance requirements.
Application Security Services from the experts of Ameya Infocom render a well-thought and thorough approach for assessing programmatic exposures, and focus primarily upon application security from the initial design stages to production deployment. Our experts evaluate business challenges together with application development practices in order to figure out the business’s most crucial areas of application susceptibility. Additionally, we provide the tools and techniques to pinpoint application security flaws and the skills to offer strategic and premeditated guidance to alleviate the overall risk.
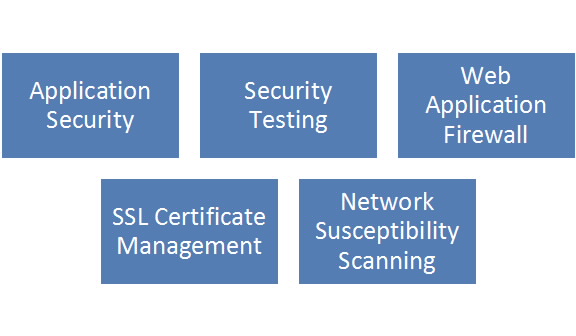
Ameya Infocom’s Application Security Services:
Product Security Assessment – Our experts will assess security of the design, code, development and implementation of service/product.
Threat Modelling & Management – We follow a collaborative approach for reckoning application threats, providing both technical and business architects the zone, where they can focus on cost and time.
Application evaluation – Our experts do the Black-box and White-box evaluation of applications against an exhaustive list of known application susceptibilities and exploits.
Secure & Safe Software Development Lifecycle Evaluation – The professionals will review the software development procedure, as well as testing and coding practices to make sure safe practices are followed at every rung of the development cycle.
Architecture Design Development – We will comprehensively review the technical architecture design in order to avoid known susceptibilities from being designed into the business applications.
Ameya Infocom Difference!
Scalable and Smart Application Security Solutions for Businesses and Service Providers
Application Security Your Way
At Ameya Infocom, we know it well that all organizations are different, and that is why we have services that are flexible, so that we can deliver as per your demands; whether it is about helping you configure, tune or install your solution so you can use it, or manage a full-fledged program for you, so you can completely focus on your business.
Sustainable
We are automation gurus. With our cloud-based management portal, you gain a real-time picture of the status of your programs, view event history, make support requests, manage your account, run reports and make support requests, all via one easy-to-use dashboard.
Enhance your Security Posture
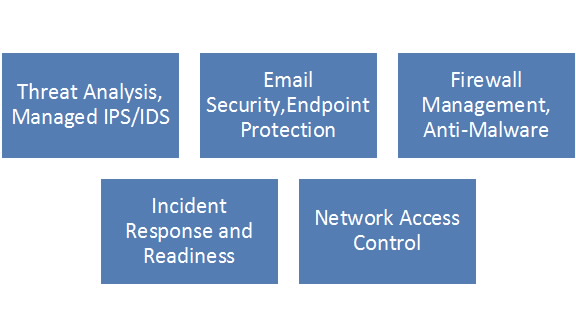
Our proficiency in high-valued application security services can definitely take you beyond the basics. We have got your firewall shielded; however, we can help you with advanced security needs as well, including, advanced anti-malware, holistic application security and self-sealing BYOD protection etc.
Growth
With a unified Ameya Infocom architecture we provide, administer and manage our own patented technologies; however, we monitor several 3rd-party products and many other widely-utilized technologies.
Leverage Intelligence
Our professionals and analysts provide you the most advanced insight and expertise. They perform threat research; analysis and interpretation that can succor you better understand, identify and avert security breaches.
24*7 Support
Our well-qualified and trained technical support engineers deliver support and satisfaction to customers round the clock